Drone identification technology is becoming the decisive factor in modern counter-UAS systems. While detection and tracking provide visibility, they do not answer the most critical operational question: what exactly is in the airspace?


Drone identification technology is becoming the decisive factor in modern counter-UAS systems. While detection and tracking provide visibility, they do not answer the most critical operational question: what exactly is in the airspace?
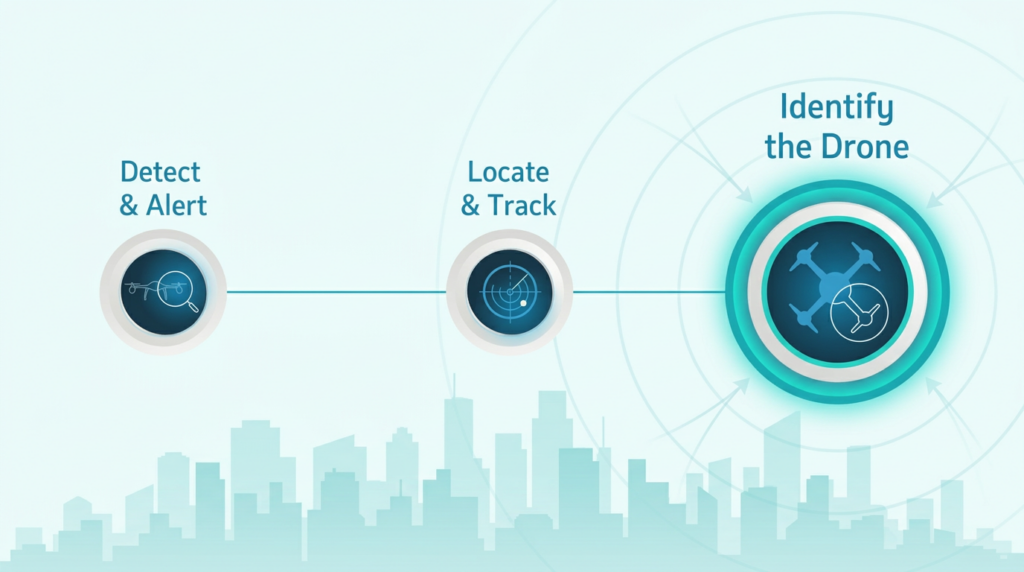
Detection, tracking, and identification (DTI) are the three core pillars of modern C-UAS airspace security. Together, they provide the real-time visibility, situational awareness, and clarity needed to manage rogue drone activity effectively. An airspace protection strategy begins with accurate detection of the threat. But detection alone is not enough. Once a drone has been identified in the airspace, precision tracking maintains ongoing situational awareness and keeps operators informed as the situation evolves. Yet even tracking has its limits. In many environments, rogue drones may enter the same airspace where authorized drones operate to support activities such as logistics, inspection, or public safety, etc. In these complex, mixed-fleet environments, clear and reliable identification becomes essential.
For both technology evaluators and front-line operators, identification is where airspace data becomes actionable operational decision-making. Detection, tracking, and identification are often discussed as separate processes. In reality, they form an interconnected framework. Without detection, tracking is impossible. Without tracking, identification lacks context and without accurate identification, response strategies risk being misguided.
Advanced C-UAS platforms bring these pillars together through smart integration, sensor fusion, and RF cyber-based insights. And yet, one of these pillars can be overlooked or undervalued. Identification is sometimes treated as an add-on benefit rather than a core capability. Read on to understand the commonly neglected “I” in “DTI” and why it deserves far greater focus from counter-drone evaluators and operators alike.
In many counter-UAS deployments, identification is the layer that turns detection data into operational decisions. The best counter-drone solution must deliver effective, precise identification– not just basic detection data. Several widely deployed technologies including radar, radio frequency/directional finders (RF/DF), and acoustic carry inherent limitations in this regard. Radar has long been a popular technology for detecting aerial drone threats, offering long-range coverage. Older legacy systems, designed primarily for military and aviation use, are adept at detecting larger aircraft but often struggle to track small unmanned aircraft systems (sUAS) due to their small size. Despite the incorporation of advanced technologies such as Electronically Scanned Array (ESA) and Micro-Doppler to improve sensitivity, differentiating small drones from other flying objects such as birds remains a persistent challenge, generating false positives and undermining reliability.
Electro-Optical/Infrared (EO/IR) sensors are typically triggered by other detection systems such as radar. However, like radar, EO/IR solutions are dependent on a clear, direct line of sight which is not always available in dense, crowded, or urban settings. Acoustic detection systems identify the unique sound signature of a drone and its motors, matching sounds against a library of known acoustic profiles. Many sensitive environments such as airports, urban centers, outdoor stadiums, and arenas are inherently loud. In these settings, drone noise can easily be drowned out and as a result, acoustic solutions are ineffective in noisy environments and cannot be relied upon for consistent identification.
For the “I” in DTI to deliver its full value, a counter-drone system must be capable of the following:
These capabilities form the benchmark for what true identification should look like in any serious C-UAS deployment.
Advanced RF cyber-based solutions offer an innovative approach to drone identification technology, employing passive, continuous scanning to detect the unique communications of commercial drones while minimizing false positives and reducing operator workload.. Once detected, the solution can classify and tag specific drones as either authorized or unauthorized. D-Fend Solutions’ EnforceAir exemplifies this approach. A high-performance anti-drone system delivering cyber-driven, non-kinetic, AI-enhanced counter-drone capabilities, EnforceAir is powered by world-leading RF cyber-takeover technology with accurate location tracking less affected by weather conditions and operates with less clear line of sight dependency than other technologies Through autonomous threat recognition, it can reduce the need for human intervention when identifying drone threats, helping to free up critical staffing resources.
The ability to identify drones is, simply put, the secret sauce of effective counter-drone operations and a core component of advanced drone identification systems, bringing capabilities that traditional detection-only technologies cannot match.
Equally important is the ability to determine both the pilot location and the home location of the drone. Knowing not just where the drone is, but where the pilot is and how their behavior is evolving in real time is crucial. For instance, if a pilot launches a drone from a home location and then begins moving in a vehicle, that behavioral pattern is a clear indicator of potential deliberate evasion. Counter-drone operators encountering such scenarios must treat the incident with heightened urgency by prioritizing the incident, committing resources to track down the pilot, and, when allowed, preparing for thorough digital forensic investigation of the drone once it has been seized.
RF-based cyber-takeover solutions make this possible by tracking the commercial drones without false positives. With EnforceAir, counter-drone operators gain access to the drone’s attributes. They can assess and prioritize the threat level of every detected drone and make informed decisions on the appropriate mitigation response. D-Fend Solutions employs a strategic, risk-based approach of analyzing, assessing, and prioritizing drones to deliver effective counter-drone mitigation. Robust identification is the foundation that makes this risk-based approach actionable, repeatable, and scalable in the field. This level of identification gives evaluators a clear benchmark for solution selection and gives operators the practical tools they need to manage repeated and evolving threats over time.
It is time for counter-drone evaluators and operators to give the “I” in DTI the attention it deserves. The ability to know exactly what’s in the airspace and act accordingly is the difference between reacting to a threat and truly taking control of the airspace.
Drone identification is the ability to determine specific details about a drone, such as its make, model, communication attributes, and whether it is authorized or unauthorized within a given airspace.
While detection and tracking provide visibility, identification enables operators to understand what the drone is and assess its threat level, allowing for informed and accurate operational decisions.
Technologies such as radar, EO/IR, and acoustic systems may struggle with accurate identification due to factors like small drone size, lack of line of sight, and noisy environments, often leading to false positives or incomplete data.
Effective identification includes recognizing drone make and model, interpreting communication signals, detecting modified drones, reading Remote ID data, and distinguishing between authorized and unauthorized drones.
RF-based solutions passively analyze drone communications to accurately identify and classify drones, reduce false positives, and provide actionable intelligence such as drone and pilot location.
Identification allows operators to whitelist trusted drones, enabling legitimate operations to continue without disruption while maintaining security over unauthorized threats.